Ping DaVinci
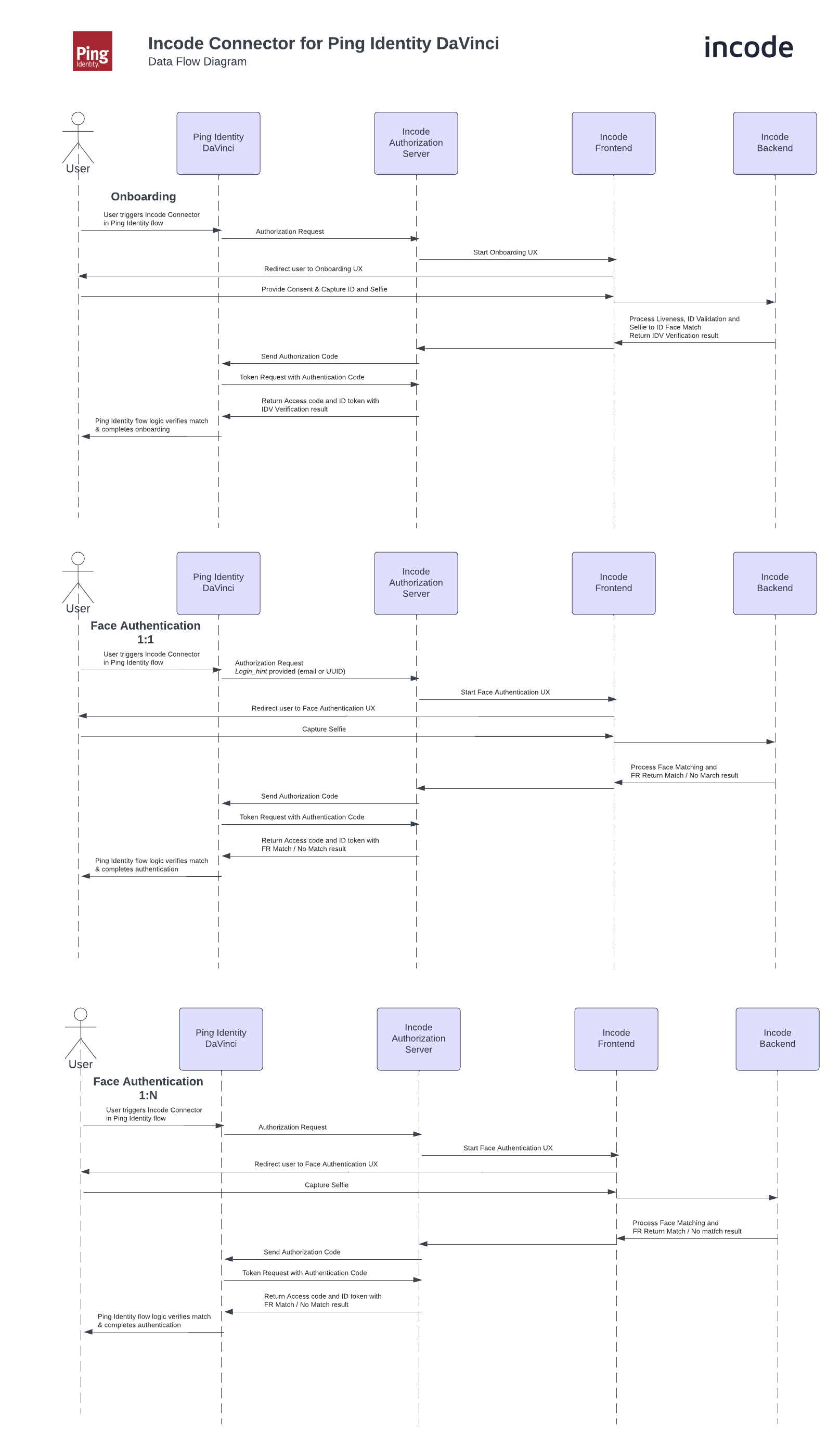
Integrate Incode identity verification into your PingOne DaVinci flows using the Incode DaVinci Connector. The connector connects verified real-world identity to Ping Identity user profiles through OpenID Connect (OIDC), enabling identity verification and face authentication as drag-and-drop nodes in DaVinci orchestration flows.
The Incode connector is published in the Ping Identity Marketplace and supports both customer identity (CIAM) and workforce identity (IAM) use cases.
Prerequisites
- A PingOne DaVinci environment with permission to add connectors
- Access to the Integrations page in Dashboard. Contact your Incode representative if you do not see the Integrations page.
- An Incode Standard Workflow configured for your verification use case
How it works
- A user reaches the Incode Connector node in your DaVinci flow.
- DaVinci redirects the user to Incode using OIDC.
- The user completes identity verification on their device — ID document capture, liveness detection, and face match.
- Incode redirects the user back to DaVinci with an authorization code and ID token containing verification claims.
- Once a user's real-world identity has been verified by Incode, face authentication can be enabled to seamlessly confirm the user's identity on subsequent flows.
Supported use cases
- User Registration: verify real-world identity as part of new user registration and create the Ping Identity user profile with verified claims
- Account Recovery: confirm identity before granting account access during recovery flows
- Password Resets: gate password resets behind biometric verification
- Conditional step-up: trigger identity verification as an additional authentication factor when risk signals are detected
Set up Guide
Step 1: Create the OIDC integration in Incode Dashboard
- Log in to Dashboard.
- In the left navigation, click Integrations.
- Click New integration.
- From the Custom tab, select OIDC, then click Continue.
- Enter a Name for this integration (e.g.
Ping DaVinci). - Configure the Redirect URI — this must match the Redirect URI in your Ping DaVinci connector configuration.
- Use the dropdown to Select a Workflow for this integration.
- Click Save. A Client ID and Client Secret are generated.
NoteThe Client Secret is shown only once. Store it securely before navigating away from this screen.
Step 2: Add the Incode connector in DaVinci
In DaVinci, add an Incode connection. For help, see the Ping documentation on Adding a connection.
Configure the connector with the following values:
| Field | Value |
|---|---|
| App ID | The Client ID from the Incode OIDC Client Configuration |
| Client Secret | The Client Secret from the Incode OIDC Client Configuration |
| Issuer URL | The Issuer URL for Incode's Authorization Server provided by Incode |
| Scope | List of space-separated scopes — must match exactly those configured in the Incode OIDC Client Configuration |
Step 3: Add the Incode Connector node to your flow
Place the Incode Connector node at the point in your DaVinci flow where identity verification should occur, typically during New User Registration so the Ping Identity user profile is created with verified claims.
Step 4: Enable face authentication (optional)
After a user has been onboarded with Incode, you can use the connector's face authentication capability in subsequent flows to seamlessly confirm the user's real-world identity without requiring another document capture.
Troubleshooting
Redirect URI mismatch
Ensure that the Redirect URI in the Incode OIDC client configuration matches the Redirect URI within the Incode Ping DaVinci connector configuration exactly.
Environment mismatch
Confirm with your Incode support representative that your account has been provisioned in the correct environment that matches the Issuer URL within the Incode Ping DaVinci connector configuration.
Additional resources
Updated 20 days ago
